The world's only Actual Private Network
CONTACT US
Securing every connection: building to building, off-site employees, point to cloud, and many more

Anything that works with TCP/IP protocol can be protected; if it plugs into the internet, we can protect it
Sensors are the foundation of network security systems; if you can’t trust your sensor data, you have no security
Encrypted sensors protect building systems, CCTV feeds, communications and additive manufacturing equipment

Modern encryption has to be non-algebraic to secure data from quantum computing. Most current encryption techniques boil down to really hard math problems and quantum computers are really good at math problems.
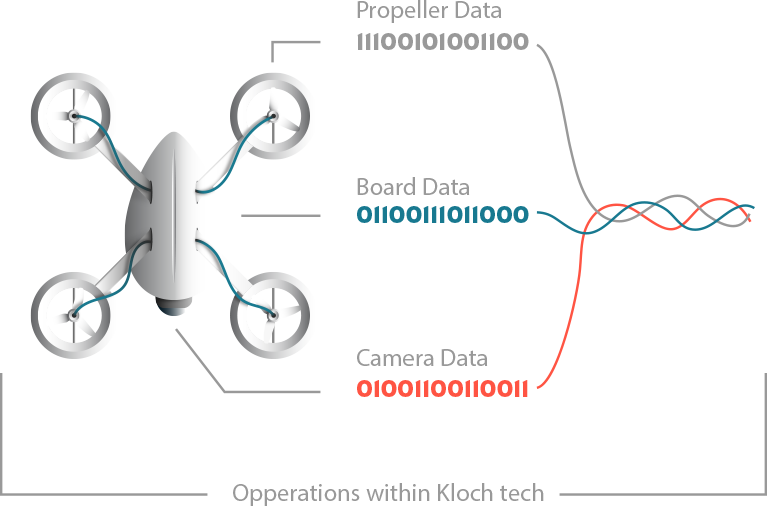
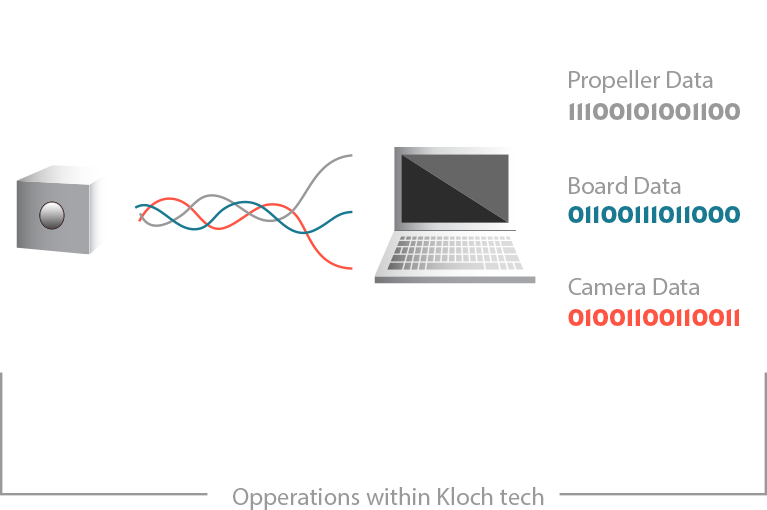
A real-time encryption method that works on the bit level is the game-changing solution the cybersecurity industry has been waiting for. Real-time gives us the ability to secure drones, video conferencing, sensors, and manufacturing equipment.
Any modern encryption technique must have ever-changing variables without any interconnectivity. The base version of our encryption has over 10512 possible variations.
Having encryption happen in an FPGA chip provides a physical barrier in a digital world. Because the system is behind our physical security, upgrades can be done in a safe manner without exposing your system.
Having the FPGA chip in an independent system removes potential software backdoors. No more worries about a printer update creating a hole in the system.


Pat Hull was a prolific entrepreneur with more than 25 years of experience launching and guiding successful companies and investments. He had a passion for marketing innovations and was responsible for leading two companies through public acquisitions.

Bryan Kane uses a simple approach to his business endeavors: networking and understanding people. Bryan is the business development for a film production studio based in NYC and has previous collaborations in the technology and entertainment arena.

Brian Penny is a musician and sound engineer. His career spans work in studios, live performance, and teaching. His obsession with sound design led to tampering with clocks to create unusual sounds. He combined binary word lengths and clocks to create Encrypted Sensors.

Founder & CEO of The Abraham Group, Inc
Business performance coach with over 10,000 clients

Chairman of Ario, LLC; Retired Mid-Atlantic Region Lead Executive, Verizon
Founding Chairman and CEO of Soulidifly Productions, LLC

Chief marketing officer at American Express
Business advisor for strategy and growth to companies from startups to Fortune 100

Dominion Energy Chief Innovation Officer
Served as chief nuclear officer and CEO at all three Dominion operating units
Chief Operating Officer of Xator Corporation
Served as member and Chairman of the CIA External Advisory Board

Martz & Associates Consulting, LLC
Advisory Board for American Corporate Partners
Cyber Defense Magazine / June 6, 2019
Virtual private networks (VPNs) have long been considered the bread-and-butter of enterprise security.
Kris Osborn / Sep 3, 2019
The age is fast emerging wherein forward-operating soldier sensors, weapons and networking technologies will all rely upon secure computing
Peter Sucio / Sep 9, 2019
Artificial (AI) or machine learning is being used by military intelligence and at the high strategic level.
Journal of Cyber Policy / Oct 27, 2019
Encrypted Sensors takes a hardware-based, non-algebraic approach to securing data.

Our encryption method is non-algebraic, happens on the binary level, is ever-changing, and lives on stand-alone hardware units to eliminate backdoors and user error.